Recommended Blogs
How does Cyber Security in Healthcare Navigate the Threat Landscape?
Table of Content
Healthcare remains one of the most targeted industries for cyberattacks, consistently reporting the highest cost per data breach across sectors. Recent estimates show that the average cost of a healthcare data breach is around $9.8 Million, significantly higher than any other industry.
The primary driver behind these attacks is financial gain, as stolen patient records enable fraud, identity theft, and unauthorized access to medical services. At the same time, human error, system intrusions, and web application vulnerabilities remain leading causes of breaches.
As healthcare systems become more connected, even minor security gaps can expose sensitive data and disrupt patient care.
The Current State of Cybersecurity in the Healthcare Sector
As cyberattacks increase daily, the FDA has announced its plan to implement new frameworks to address the safety issues of medical devices. These frameworks could assist in protecting consumer data and improving the cyber security of medical devices. The FDA’s medical device safety plan focuses on how stakeholders can enhance their processes to ensure medical device safety. Seeing the rapid digital transformation to offer personalized and improved CX, ensuring the safety of healthcare applications and devices is a major concern for industry leaders.
Security threats and data breaches are paramount in the healthcare industries. Attacks are usually successful because of loopholes in the infrastructure, compromising life-critical consumer data. A couple of years back, The WannaCry Ransomware attack almost impaled the UK National Health Service. It would have been a disastrous incident for healthcare operators if there had been a slight delay in the action plan. This is just one example of cyberattacks against the medical sector. Hackers are also targeting EHR vendors, simultaneously threatening various enterprises’ functionalities.
The user remotely controls sensitive devices that connect with the brain or heart. Just imagine what would happen if the device key that controls the organ functionalities gets leaked. In the worst-case scenario, it would result in the patient’s death if it fell into the hands of a person with malicious intent. Although it may sound like a scene from a TV drama, everything is possible in the current digital age. Such outcomes would have an everlasting impact on healthcare organizations.
Key Factors Driving Cyber Security in Healthcare
Compared to other industries, healthcare faces a complex cyber threat landscape. The dependency on digital systems to handle patients and their details is increasing, which raises the bar for robust cyber security protocols. In addition to securing sensitive data, healthcare organizations must comply with regulations to ensure patient safety.
Let’s take a close look at the key factors driving cyber security in the healthcare sector:
Increase in Cyberattacks:
Hackers’ main target in recent cyberattacks has been medical records containing personal information. These records are sold for a hefty amount on the dark web and can be used for identity theft. Whether it’s a medical device or a healthcare app/website, hackers target everything that could help them obtain such vital information. This pushes healthcare providers to enhance their security defenses against ransomware and other cyberattacks.
Healthcare Digital Transformation:
Electronic health records (EHRs), cloud computing, and telemedicine are some of the components responsible for digital transformation in the healthcare sector. Although these technologies introduced various benefits, they also raised new security challenges. And this is not the end of it. With new tech innovations, this sector will become more digitized, making it necessary to implement robust security measures to secure sensitive data and ensure care continuity.
Changing Cyber Threat Landscape:
Cyber threats are becoming more sophisticated and harder to crack. Zero-day vulnerabilities and Advanced Persistent Threats (APTs) are some of the major concerns for healthcare professionals. Here, the need is to stay one step ahead of such threats by opting for and implementing advanced cyber security technologies and practices.
IoT Devices Integration in Healthcare:
IoT device integration enables healthcare practitioners to improve patient care by providing real-time health monitoring. However, they also introduce new security challenges due to their weak security protocols, making them easy targets for hackers. It is necessary to secure these devices to ensure the integrity of medical treatments.
Regulatory Compliance:
Enterprises selling healthcare products (apps, websites, medical devices) must comply with various regulations, such as GDPR and HIPAA. These regulations also vary region-wise. Noncompliance can result in hefty fines and a bad reputation, driving healthcare providers to implement comprehensive cyber security strategies.
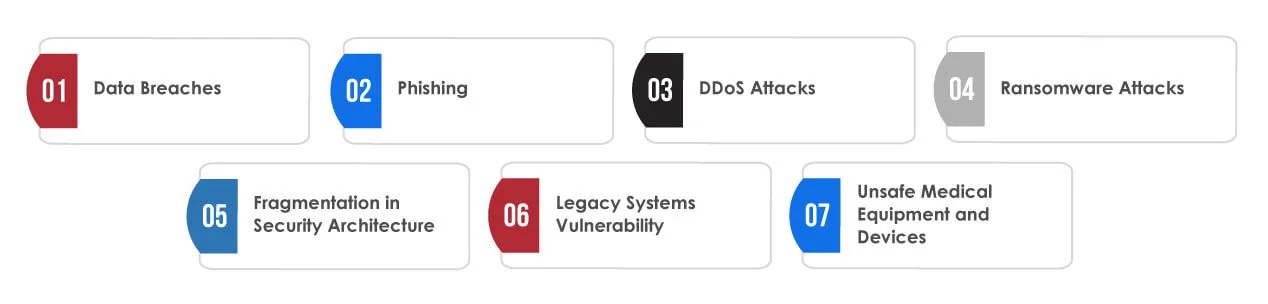
7 Cyber Threats in the Healthcare Sector
Poor cyber security practices, compromised data storage, and underhanded tactics to ensure business continuity make healthcare organizations prime targets of hackers. The 7 biggest challenges below highlight the urgency of healthcare cyber security measures within the current threat landscape. They pose the greatest risk to patient data and information security.
Data Breaches:
Compared to other industries, the healthcare sector suffers the most from data breach attacks. Sometimes, health entities struggle to implement security controls, leaving gaps in the entry points and threatening the security of patient care data. Despite implementing HIPAA requirements, they still struggle with data breaches.
Phishing:
Phishing is one of the most common security threats that infect an innocuous email with malicious links. It is one of the most common methods attackers use these days. These emails look very convincing, raising the urgency for a medical disturbance to incentivize link-clicking. Some advanced hackers even compose thorough emails consisting of replies and email threads to deepen the authenticity and minimize suspicion of email.
DDoS Attacks:
In a DDoS attack, many fake connection requests are sent to the targeted server, forcing it to shut down. Multiple endpoints and IoT devices are integrated into the botnet via a malware infection to engage in a coordinated attack. DDoS attacks can achieve the same disturbance as ransomware attacks without compromising a network and can be deployed on a wider scale.
Ransomware Attacks:
In this attack, hackers inject malware into the network to infect and collect sensitive data until the victim pays the ransom. The primary method used to inject malicious software is a phishing attack. The growing number of ransomware attacks is also due to the new tech innovation automating these attacks. Even better, hackers have created their version, the Ransomware-as-a-Service model, inspired by the Business-as-a-Service model.
Fragmentation in Security Architecture:
Healthcare organizations commonly do not bother with their cyber security program. Instead, they deploy an array of point security products. According to data, almost 80% of healthcare entities depend on ten-point products for security. This creates difficulties in identifying and mitigating potential attacks before hackers can access or deploy ransomware within the organization’s IT systems.
Legacy Systems Vulnerability:
Most healthcare organizations still work with legacy systems (outdated workstations and networked medical equipment). These systems contain unpatched vulnerabilities that make them an easy and prime target for hackers to exploit.
Unsafe Medical Equipment and Devices:
IoMT is the rising trend among healthcare organizations, showing the growing dependency on networked devices. Like IoT devices, IoMT systems have poor security and multiple weak points that hackers exploit to gain unauthorized access to the systems and sensitive data.
Summary
The healthcare industry faces immense cyber threats, and implementing robust security protocols has become essential. Healthcare organizations are experiencing frequent data breach incidents in which hackers’ main target is valuable patient records. IoT device integrations, regulatory compliance, and digital transformation are some aspects that add complexity to securing healthcare data. Poor cyber security practices, fragmented architecture, and legacy systems increase risks. Partnering with Tx can help you protect your patient data, ensure compliance, and secure healthcare apps and devices against evolving threats. To know more, contact our cybersecurity experts now.
FAQs
AI finds unusual behavior, predicts ransomware tendencies, automates triage, and speeds up response time. It makes proactive protection stronger in the EHR, cloud, and IoMT ecosystems.
- HIPAA for U.S. healthcare data protection
- GDPR for EU patient data privacy
- ISO 27001 for information security management
- NIST CSF for structured risk governance
Keep an eye on lower breach costs, less downtime, better compliance audit scores, faster response times to incidents, and fewer legal penalties.
Real-time warnings, automated threat correlation, and quick patch management help stop attacks before they turn into full-blown breaches.
TestingXperts uses AI to find threats, check for compliance, and keep an eye on things all the time to keep healthcare apps safe without getting in the way of patient services or clinical workflows.
Discover more